Mastering Disaster Recovery - Part 4 - Offsite & Offline Backups
As a software engineer with 5 years of experience, I work on the core backup & recovery features of Zmanda, an enterprise backup and recovery product. I have strong skills in software design, cloud-native development, and delivery. I also foster effective communication and collaboration among the development team, architects, product owners, and business owners. I contribute to some open-source projects and share my technical insights on my blog.
They both solve different problems
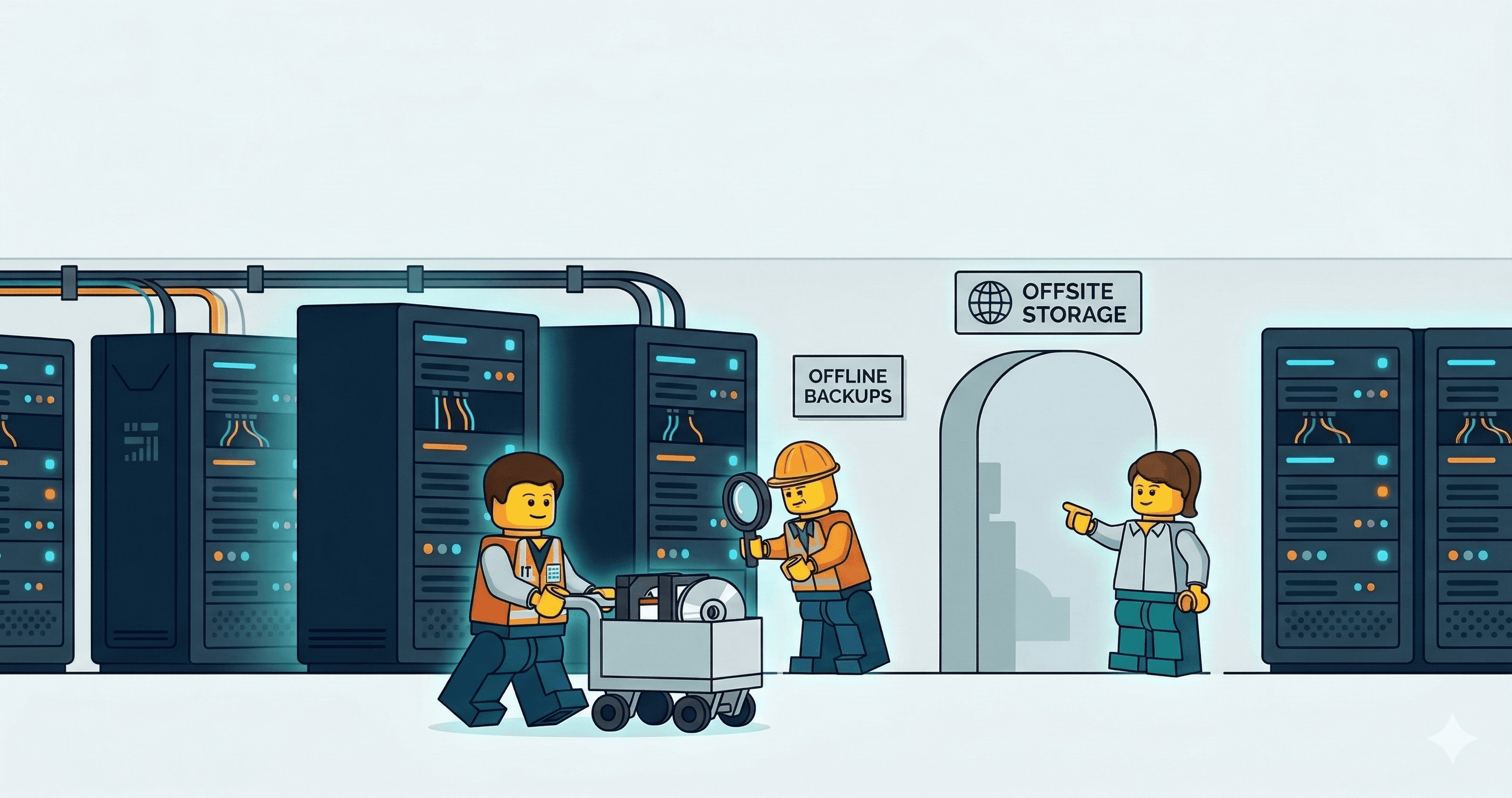
Offline and Offsite backup and disaster recovery is often confused as the same thing. Both terms describe data locality but are designed to address different risk in an organization's disaster recovery posture.
What are offline backups?
Offline backup involves storing data on a storage medium disconnected from the network such as a tape drive or an external HDD. It is also called “air-gapped backup” because it’s not reachable by any running software.
What are offsite backups?
Offsite backups on the other hand is data stored at a different physical location than the primary data. Offsite backup copies help provide redundancy and improve availability of data. They provide protection against disasters like fires, power outage or natural disasters in the primary site.
The overlap
These concepts can overlap:
A backup can be offsite but still online — for example, a cloud replica that is network-accessible.
A backup can be offline but still onsite — for example, a tape stored in a cabinet at the primary site.
To maximize resilience, enterprises must focus on combining both Offline and Offsite backups.
Example: a weekly backup is copied from the primary site to a secondary site over the network. The secondary site then writes that copy to an air-gapped medium (e.g., tape) and retains it in a physically separate location. This approach protects against both localized site failures and network-based threats.
Upgrading the resiliency of your 3-2-1 backup strategy
The 3-2-1 backup strategy requires three copies of data, on two different media types, with one copy stored offsite. The most resilient way to implement 3-2-1 is to make the third copy both offline and offsite. The primary data lives on production storage. The second copy is a disk-based backup kept onsite for fast restores. The third copy is a weekly backup sent to a secondary site and written to a tape drive or external HDD. After the backup is completed the tape drive or HDD is disconnected from the network.
Threat 1: Hardware and Media Failure
Hardware failure is the most common threat to data. Drives fail, storage controllers malfunction and tapes degrade over time.
Mitigation: An offline copy is protected from cascading hardware failures. A firmware bug that bricks an entire storage array cannot reach a backup that is disconnected. An offsite copy adds further protection. If the failure is caused by a local issue like overheating or unstable power a copy at a different location is not affected.
Threat 2: Human Error and Data Corruption
A misconfigured script can overwrite production data. An application bug can corrupt a database silently over weeks. These failures are dangerous because they propagate. A corrupted database gets replicated to every connected backup target.
Mitigation: Offline backups break this chain. They preserve the state of the data at the point the backup was taken. If corruption has been spreading for days the offline copy from last week may be the only clean version that exists.
Threat 3: Ransomware and Cyber Threats
Modern ransomware does not just encrypt production data. It actively searches for backups. Network-attached backup shares and cloud-synced repositories are all targets.
Mitigation: An air-gapped copy such as a tape in a vault or a disconnected drive is not reachable by malware. There is no network path to it. Offsite backups add protection against insider threats. An employee with administrative access to local systems cannot destroy backups at a remote facility they cannot physically access.
Threat 3.1 Correlated Failures
The real risk is when a single event compromises multiple copies at once. Ransomware encrypts production data and the network-attached backup. A fire destroys the server room and the backup drives next to it.
Mitigation: Offline breaks the network link so cyber threats cannot propagate to every copy. Offsite breaks the geographic link so physical events cannot affect every copy. Together they create a backup that is digitally unreachable and physically distant.
Threat 4: Site-Level Disasters
Fire, flood or prolonged power outage can destroy everything in a single location. It does not matter how many backup copies exist if they are all in the same building.
Mitigation: Offsite backups solve this. A copy at a different geographic location ensures a localized disaster cannot wipe out all copies of the data. When combined with offline storage there is an added benefit. A disaster that takes out network connectivity can leave cloud-based offsite backups unreachable. A physical offline copy at a remote facility is available regardless of network conditions.
The 3-2-1-1-0 strategy and beyond
It is beneficial to extend this to build the 3-2-1-1-0 strategy where the extra "1" explicitly requires one copy to be offline or immutable and the “0” explicitly requires a zero errors copy. This makes the air gap a formal part of the backup policy. Backup tools and policies must be configured to ensure that only a backup with zero errors is moved to the offline copy.
Conclusion
In my experience making customers understand the difference between offline and offsite backups has been very critical while also explaining the importance of implementing both. Achieving whatever I have mentioned in this blog for both offsite and offline backups is very challenging in large organizations. I will continue to explore the world of backup and disaster recovery and come back with more practical insights in the future.